Vulnerabilities in systems or websites are found every day by security researchers, ethical hackers, tech hobbyists, journalists, academics, and even customers themselves. It would be advantageous for external parties who come across bugs to have guidance in reporting vulnerabilities -- good thing there is the Vulnerability Disclosure Policy or VDP.
Vulnerability Disclosure Policy
The Vulnerability Disclosure Policy or VDP is the equivalent of “if you see something, say something” that helps organizations to receive, coordinate, and act on security vulnerability submissions from cybersecurity professionals or security researchers through their Vulnerability Disclosure Program.
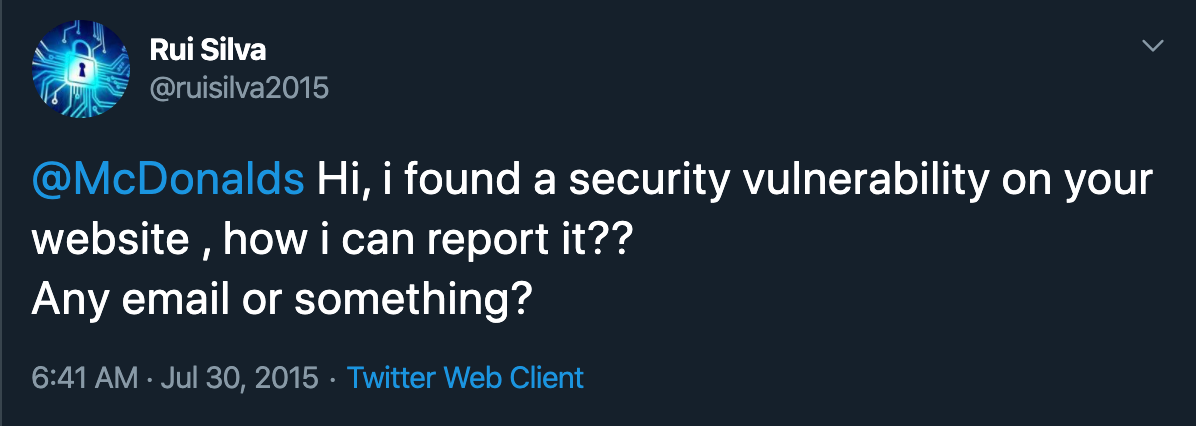
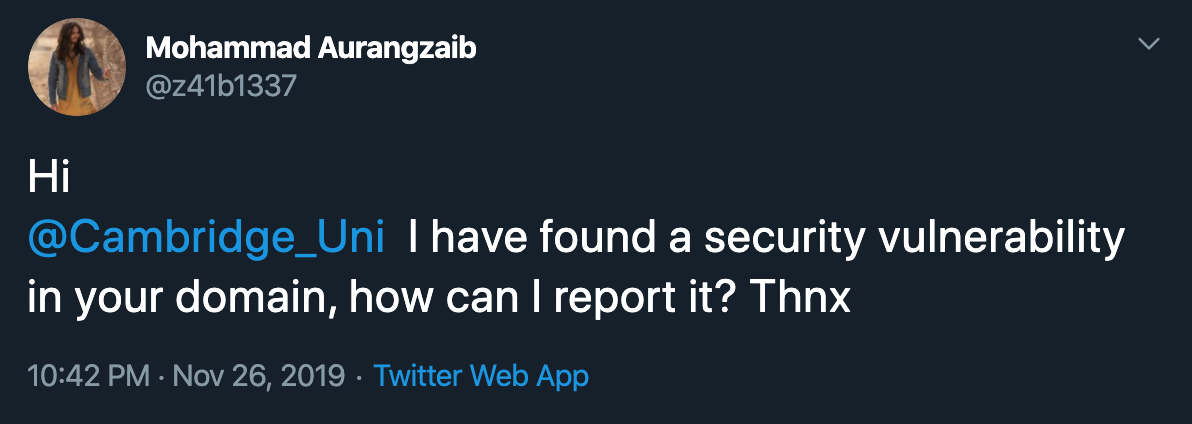
Unfortunately, researchers who couldn't find an avenue to report the vulnerability tends to disclose it publicly through social media and simply tag the account of the concerned organization.

With VDP, Security Researchers are given clear guidelines or direction for submitting potentially unknown and harmful security vulnerabilities to an organization. This also eliminates the potential PR nightmare for your organization by giving your internal cybersecurity team a proper way to receive and act to such reports.
The New Standard in Cybersecurity
Running a Vulnerability Disclosure Program is an effective approach in fighting cybercrime and an efficient tool in protecting systems as well as its users from cyberattacks. Since 2017, different government and industry organizations have developed and released templates, frameworks, standards, and comments on how to properly address VDPs. This includes the U.S. Federal Trade Commission (FTC), Department of Justice (DOJ), ISO/IEC 29147:2018, 18F Vulnerability Disclosure Handbook and National Institute of Standards and Technology.
Must Have Components in a VDP
The following components listed and explained below are essential in building a Vulnerability Disclosure Policy.
- Guideline and Expectation - Contains a list of general requirements for security researchers when reporting a potential vulnerability to an organization and a promise of commitment to collaborate with security researchers.
- Vulnerability and Asset Scope - Specifies the vulnerabilities and assets (applications) that are covered in a program. For clarity, this section should include both what is in-scope and what is out-of-scope. Organizations may choose to keep certain systems or products off-limits to protect their system or customer data.
- Safe Harbor - Assures that reporters of good faith are authorized and will not be unduly penalized during the engagement.
- Process - Dictates how a reported vulnerability will be validated and coordinated for remediation.
As an example, we at Secuna, have published our very own VDP.
Voices of Experts and Market Leaders
Art Carter - Former U.S. Secretary of Defense, Department of Defense (DoD)
"For the first time, anyone who identifies a security issue on a DoD (Department of Defense) website will have clear guidance on how to disclose that vulnerability in a safe, secure, and legal way."
Rod Rosenstein - Deputy Attorney General, Department of Justice (DoJ)
"All companies should consider promulgating a vulnerability disclosure policy, that is, a public invitation for white hat security researchers to report vulnerabilities found on your system.”
Jeff Massimilla - Vice President Global Cybersecurity, GM
"To improve the security of their connected systems, every corporation should have a vulnerability disclosure policy that allows them to receive security submissions from the outside world."
Tobias Lütke - CEO, Shopify
"One of the best ways for us to augment our internal security team is to work with the white hat community."
Launching a Vulnerability Disclosure Program on Secuna
As you learn the importance, benefits, and security that VDP can bring to your organization, you may want to get started by signing up to Secuna. Below are the steps you can use to prepare your VDP.
- Get Everyone Involved
Inform and consult the different teams as much as possible from the Information Security, Engineering, Product, Marketing, and Executive as well as the Legal in every process of your VDP from the development of the policy up to resolving a vulnerability.
- Information Security Team.
Communicates with security researchers in validating and evaluating the security vulnerability reports.
- Engineering Team.
Plans and remediates in collaboration with Information Security and Product teams.
- Product Team.
Securely designs the UI and UX of the application.
- Marketing Team.
Should be aware of public disclosures that might impact the brand and reputation of the organization and its products.
- Executive and Legal Team.
Must be informed on the vulnerability in case of a potential security and data breach. - Draft a Clear and Researcher-Friendly Policy
VDP for a program need not to be long and wordy. (Refer to Must Have Components in a VDP above) - Find a Secure Platform with a Pool of Trusted Security Researchers
Secuna Discover offers a Basic (that is FREE) and Pro (via Subscription) plans for Non Profit Organization, Open Source Projects, Startups, and SMEs to run their Vulnerability Disclosure Program. These plans allow receipt and proper management of potential security vulnerabilities that are fully compliant to ISO/IEC 30111: 2019 (Vulnerability handling processes).
To learn more about our programs and platform, visit and contact Secuna today!
Secuna is a trusted cybersecurity testing platform that provides organizations a robust and secure platform that enables them to collaborate with the top security researchers from around the world to find and address security vulnerabilities.
